In this blog we will go over replacing the LocalManager certificate in NSX. In this example I will be using the UI to generate the self signed certificate and then an API call to replace the certificate.
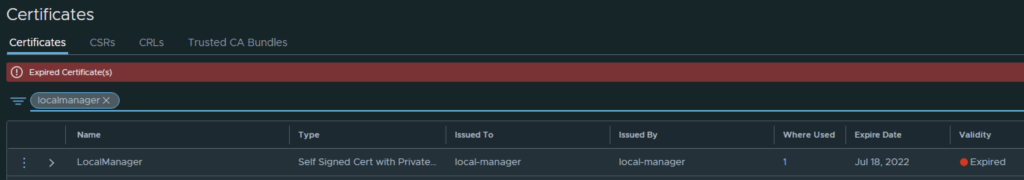
In my case the LocalManager certificate has already expired
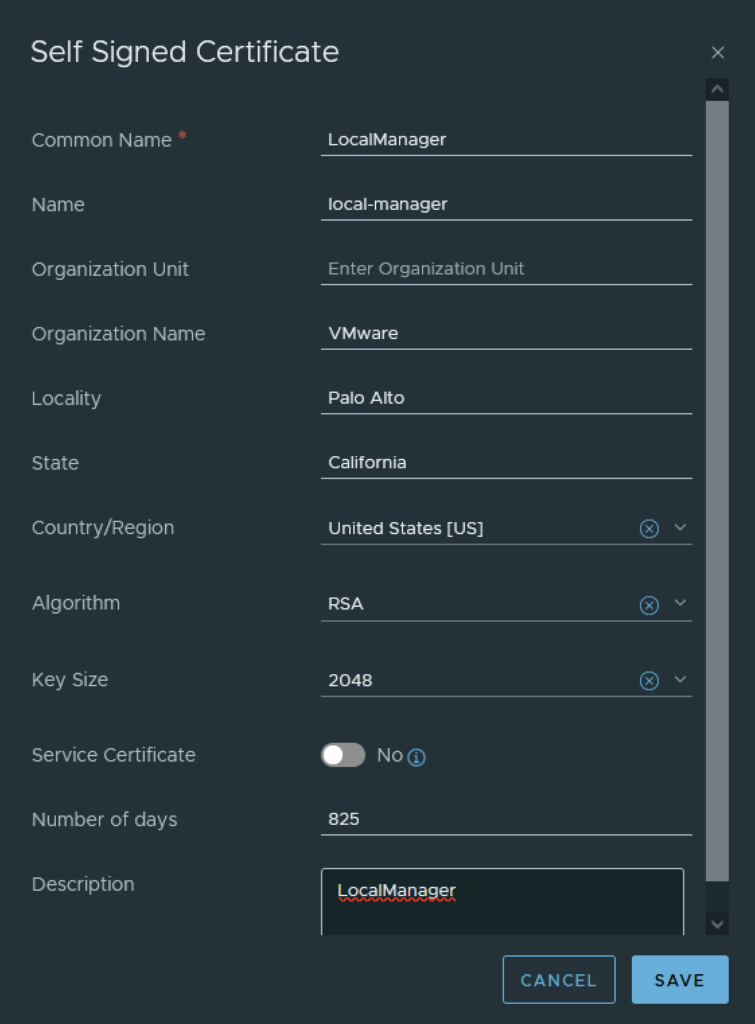
In the top menu bar I went to Generate -> Generate Self Signed Certificate
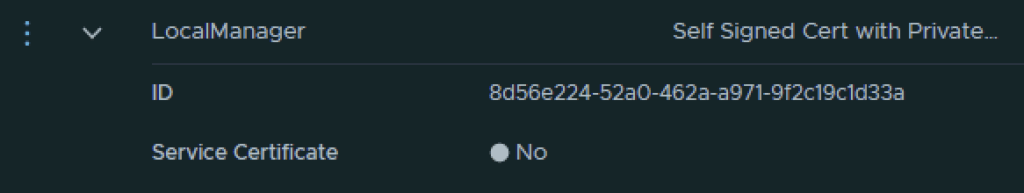
Next I had to grab the new certificate ID
The next step is to replace the old certificate with the new certificate via an API call. For this I used Postman but any other tool could potentially be used.
The URL for the post call would go against https://nsx_fqdn/api/v1/trust-management/certificates?action=set_pi_certificate_for_federation
For authentication I used basic, per best practices we should be using a token.
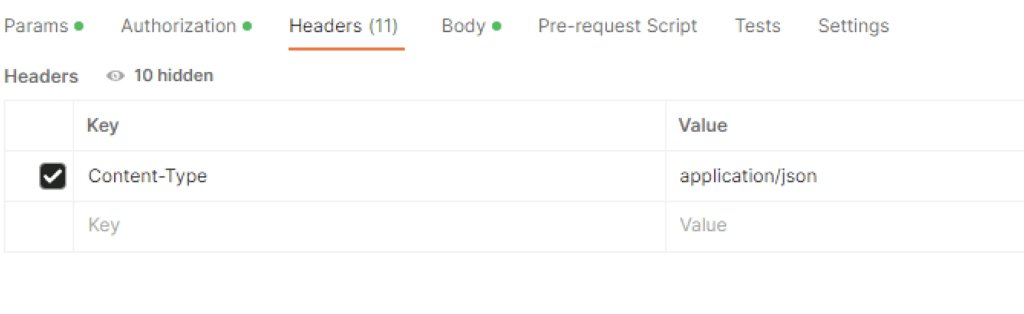
For headers had to add Content-Type application\json ex
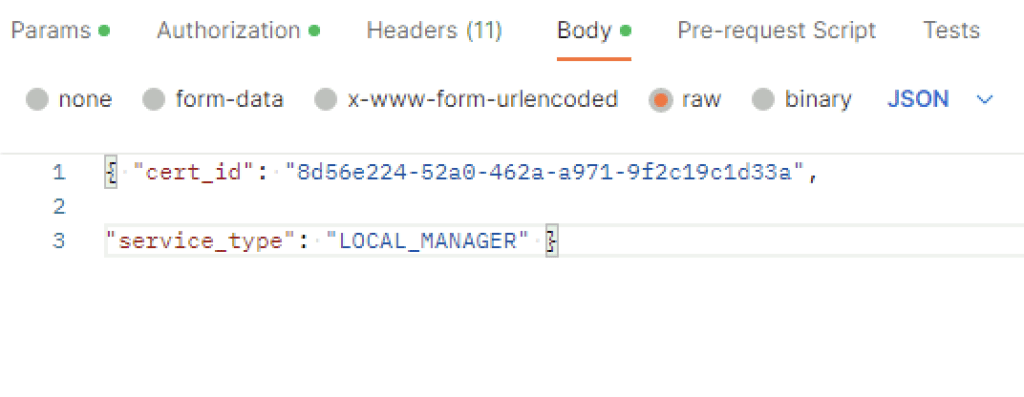
In the body I picket raw and added the following in
{ "cert_id": "8d56e224-52a0-462a-a971-9f2c19c1d33a",
"service_type": "LOCAL_MANAGER" }
The cert ID is from the certificate I generated earlier. ex
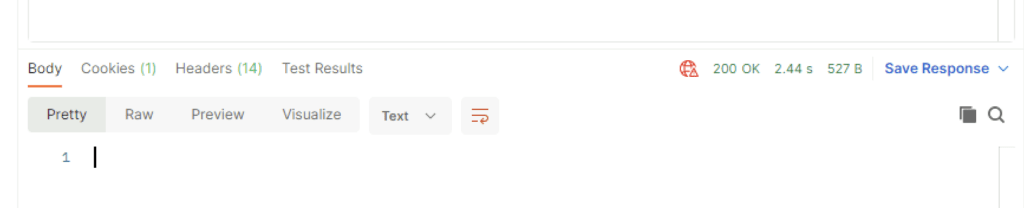
Once I clicked send I was presented back with a 200 OK
Going in the web browser I can also see that the new certificate is now used and the old one doesn’t have anything assigned to it ex
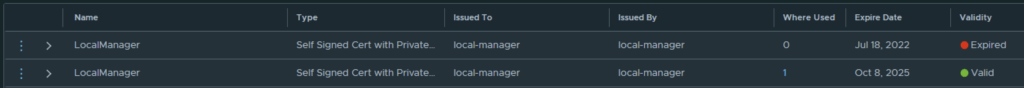
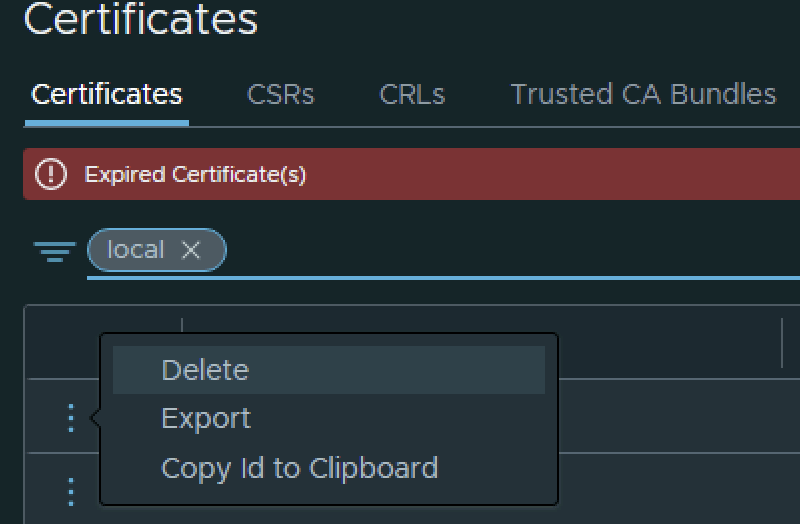
The final step I did was removing the old certificate by clicking on the 3 dots to left and picking delete from the menu